(Last edited: November 23, 2015)
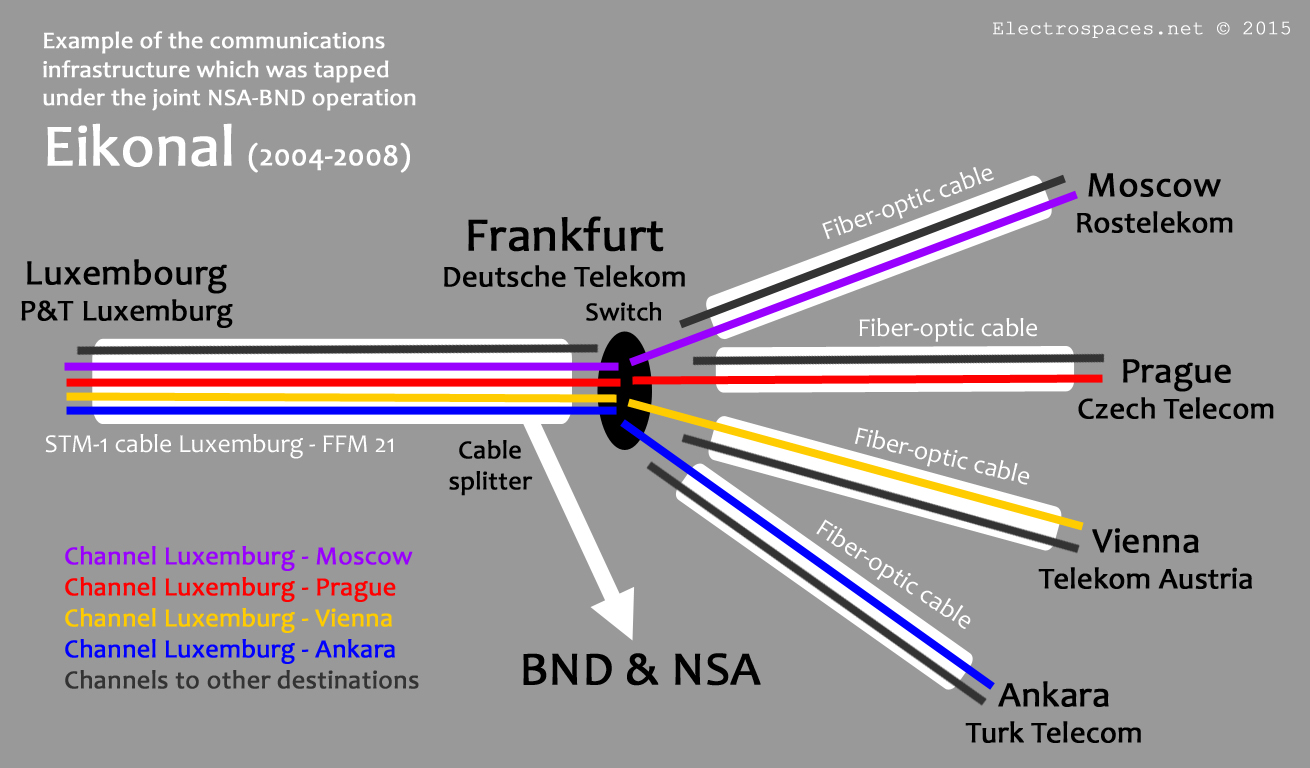
Almost unnoticed, the Austrian member of parliament Peter Pilz recently disclosed new information about operation Eikonal, under which NSA and BND cooperated in tapping some fiber-optic cables at a switching center of Deutsche Telekom in Frankfurt, Germany.
As part of the NSA umbrella program http://lasvegasin.blogspot.com /2014/10/the-german-operation-eikonal-as-part-of.html#rampart-a">RAMPART-A, Eikonal was set up to gather intelligence about targets from Russia, the Middle East and North-Africa. Because the cables that were tapped came also from countries like Austria, Switzerland, France, Belgium and the Netherlands, there were fears that their communications were intercepted too.
Here, the newly disclosed information will be discussed and combined with things we learned from the hearings of the German parliamentary commission that investigates NSA spying, including operation Eikonal.
> See also: http://lasvegasin.blogspot.com /2015/05/new-details-about-joint-nsa-bnd.html">New details about the joint NSA-BND operation Eikonal
Leak
The new information comes from transcripts of some fax and e-mail messages from employees of BND, Deutsche Telekom and the federal Chancellery, which Peter Pilz published on his website on October 23, 2015.
He never told how he got these highly sensitive documents, but as they were made available to the parliamentary inquiry commission, it seems most likely someone from or very close to this commission must have leaked them to Pilz. Strangely enough, this leak was never investigated.
Media attention
Also remarkable is that the information and documents disclosed by Peter Pilz were almost completely ignored by mainstream German media like ARD and ZDF and the major newspapers. The latest disclosure was for example only reported by the Austrian paper Der Standard and the German tech website Heise.de.
By contrast, in neighbouring countries like Austria, Belgium and the Netherlands, the Pilz revelations were big news and led to official investigations. Through May and June of this year, he had published lists of communication links related to Switzerland, France, Luxembourg and Poland too, claiming they showed to what extent BND and NSA spied upon these countries.

First part of the list with communication links related to France
(Source: Peter Pilz - Click to enlarge)
Whose's links?
Initially, Peter Pilz claimed these links were from a priority list of the NSA, but neither he, nor the commission hearings could clearly confirm this. The Dutch website De Correspondent reported that there was even a much larger list of some 1000 transit links, of which ca. 250 were marked in yellow.
Now, Pilz confirms that there's indeed such a large list: it was prepared by Deutsche Telekom and contains all its 1028 transit links. Employees of BND had marked 256 of them in yellow, apparently the ones they were most interested in, and hence the list became known as the BND priority list. He doesn't mention an involvement of NSA at this stage anymore.
Now that we know the large list of over 1000 links isn't an even larger "wish list", but a list of all available transit links, it could well be that BND tried to select around 20% of them, as a rather strange provision in German law says that bulk collection is only allowed up to a maximum of 20% of a cable's capacity.
As Telekom Austria rented the channels to Vienna, we can assume that other national telecommunication providers also rented their links to Frankfurt, with Deutsche Telekom being the owner of the cables as part of their international backbone network.
Determining the access points
After BND selected the 256 channels, Deutsche Telekom had to look which of them ran through Frankfurt and could be intercepted there. For this purpose Harald Helfrich of the lawful interception unit of Deutsche Telekom AG (DTAG) sent his collegue mr. Tieger the following e-mail on September 16, 2003:
Hallo LK,
wie heute morgen besprochen übersende ich Ihnen die Liste der Transit-Leitungen der DTAG. Wir bitten Sie die gelb unterlegten Verbindungen bzgl. ihrer Führung (z.B. Ffm 21 oder Norden-Nordeich) und ob in der 2-Mb-Ebene greifbar, zu analysieren.
Anlage: Trans mit ausgesuchten Strecken
In this mail it is asked to analyse whether the transit channels marked in yellow can be intercepted at the 2 Mbit-level, either at Deutsche Telekom's Frankfurt am Main Point-of-Presence 21 (Ffm 21) or at Norden-Norddeich.
The latter is a town at the northern coast of Germany, where the SeaMeWe-3 and TAT-14 submarine cables land. For the parliamentary commission this was a reason to ask whether also cables where intercepted over there, but that was strongly denied by the witnesses involved.
Selecting individual channels?
Interestingly, the phrase "ob in der 2-Mb-Ebene greifbar" suggests that it could be possible to just intercept specific 2 Mbit/s channels while leaving the other ones untouched (one physical STM1-cable has a data rate of 155 Mbit/s and contains 63 virtual channels).
Whether this is possible is important for how focused such cable tapping can be. Isolating individual channels depends in the first place on where exactly the tapping takes place:
A. When the physical fiber is intercepted before it reaches the switch, it has to be bend in order to catch the light that leaks. Because this leaking signal is much weaker, it has to be amplified before it can be processed. In this way it's not possible to select individual channels: the eavesdropper gets everything that runs over the fiber, and has to demultiplex the channels himself to select the ones that contain traffic of interest.
Splitting a traffic from a fiber-optic cable by bowing it
(diagram: OSA Publishing, slightly simplified)
B. When the interception takes place at an optical switch itself, then it's possible to only grab the virtual channels you are interested in. A physical cable contains channels which have to be demultiplexed at the switch in order to be forwarded (switched) to the fiber that leads to the intended destination. When the switch converts the optical signals into electronic signals it is even more easy to duplicate only individual channels of interest.

Diagram showing (de)multiplexing at a fiber-optic switch
(diagram modified from Wikimedia Commons/Jflabourdette)
Different methods
During the commission hearing of March 26, 2015, Klaus Landefeld, board member of the DE-CIX internet exchange, indicated that at least since 2009, interception takes place at the switch. Also, the so-called G10-orders authorise interception based upon Autonomous System Numbers (ASN) which are used for logical paths, rather than by naming physical cables to or from a certain city.
However, it seems that under operation Eikonal, the fiber-optic cables were tapped by splitting the cable signal before it reached the switch. This was more or less clearly indicated by several witnesses heard by the parliamentary commission, and there are several other indications too.
In 2004, it was apparently not yet possible to establish a tap at the switch itself to get access to individual channels (although Deutsche Telekom could have demultiplexed the fiber and only forward the channels of interest to BND, but this wasn't the case).
Government authorisation
After BND had made clear what they wanted, the Deutsche Telekom management wasn't sure whether such cable access was legal. Therefore they wanted to be backed by the federal Chancellery. On December 30, 2003, the coordinator for the intelligence services at the Chancellery, Ernst Uhrlau, sent the following fax message to Kai-Uwe Ricke, then CEO of Deutsche Telekom, and Josef Brauner, head of the landline division T-Com:
Sehr geehrter Herr Ricke, sehr geehrter Herr Brauner,
das Bundeskanzleramt ist sehr interessiert, dass der Bundesnachrichtendienst im Rahmen seines gesetzlichen Auftrages kabelgestützte Transitverkehre aufklärt. Der vom Bundesnachrichtendienst in Ihrem Unternehmen geplante Aufklärungsansatz steht aus hiesiger Sicht in Einklang mit geltendem Recht.
Ich darf auf diesem Weg die Anregung des Bundesnachrichtendienstes weitergeben, in der Deutschen Telekom AG, T-Com, den Bereich RA 43 (Staatliche Sonderauflagen), zu dem bereits im Rahmen der Strategischen Fernmeldekontrolle Kontakte bestehen, mit der Durchführung der auf Seiten der Deutschen Telekom AG erforderlichen Maßnahmen zu beauftragen.
It says that in the opinion of the Chancellery, the proposed BND operation is according to German law. The Chancellery encourages Deutsche Telekom to instruct its lawful intercept unit RA 43 (which is one of four Regionalstellen für staatliche Sonderauflagen or ReSA) to start taking the necessary measures for the interception.
Transit Agreement
On behalf of the board of Deutsche Telekom, Josef Brauner answers the fax from the Chancellery on January 13, 2004. He says the T-Com division is aware of the importance of a well-functioning intelligence service, and will therefore support the interception of cable-bound transit traffic:
Sehr geehrter Herr Ministerialdirektor,
gerne bestätigen wir Ihnen den Erhalt Ihres Schreibens vom 30. Dezember des letzten Jahres.
Die T-Com ist sich der Bedeutung eines gut funktionierenden Nachrichtendienstes für das Gemeinwesen der Bundesrepublik Deutschland - insbesondere vor dem Hintergrund der terroristischen Angriffe des 11. September 2001 - bewusst und wird daher die geplanten Aktivitäten des Bundesnachrichtendienstes, die kabelgestützten Transitverkehre im Rahmen seines gesetzlichen Auftrages aufzuklären, unterstützen.
Entsprechend der Anregung des Bundesnachrichtendienstes wird diesseits unser Bereich RA43 (staatliche Sonderauflagen) beauftragt, die hierfür von unserer Seite erforderlichen Maßnahmen vorzunehmen
Then on March 1, 2004, the BND and Deutsche Telekom signed the so-called Transit Agreement (pdf), in which the latter agreed to provide access to its transit cables, and in return will be paid 6.500,- euro a month for the expenses. This agreement was also leaked to Peter Pilz, who published it on May 18, 2015 in the Austrian tabloid paper Kronen Zeitung.
Preparing for collection
After the agreement had been signed, BND sent an e-mail on March 9, 2004 to Wolfgang Alster, head of Deutsche Telekom's lawful interception unit RA 43 asking for the connection (schaltung) of the first communication links. He adds that he had ordered the payment of the first two monthly payments:
Schaltauftrag
DTAG RA 433
Hallo Herr Alster,
Der Geschäftsbesorgungsvertrag "Transit" ist ja jetzt von beiden Seiten unterzeichnet und gestern habe ich die beiden ersten Monatszahlungen veranlasst.
Daher erdreiste ich mich, Sie um die erste Schaltung von Leitungen zu bitten.
Realising the access was apparently not that easy, because it took until December 2004 before the first cable was connected. Then it appeared that it's signal was too weak, so in January 2005 an amplifier was installed - as the parliamentary commission was told by S.L., who was the BND project manager for Eikonal (note that the use of an amplifier indicates tapping the entire fiber-optic cable).
At this first stage of operation Eikonal, only circuit-switched (Leitungsvermittelte) telephone communications were intercepted. Collection of packet-switched (Paketvermittelte) internet communications started in 2006 (see below).
RUBIN
On February 3, 2005, mr. Knau mailed his colleague Harald Helfrich at the RA 43 unit that an STM1-link between switching center Frankfurt 21 and Luxembourg had been connected. Channels 2, 6, 14, and 50 contained the virtual channels that had Luxembourg as their endpoint:
Hallo Herr Helfrich,
Habe heute früh die o.g. Verbindung auf die Punkte 71/00/002/03 19 + 39 zugeschaltet. In der Anlage ist die Belegung lt. RUBIN ersichtlich.
Auf den Kanälen 2, 6, 14, 50 befinden sich die in der Liste markierten DSVn mit der Endstelle Luxembourg.
Bitte um Rückmeldung ob das ganze funktioniert.
Anlage: Belegung 7571 Luxbg
We also see the term RUBIN (German for ruby), and during the commission hearings it seemed that this was an alternate codename for operation Eikonal. But when heard on January 15, 2015, Harald Helfrich explained that RUBIN is actually a system that Deutsche Telekom uses to manage its communication links and cables - which perfectly fits how the term is used in this e-mail.
Channels of interest
The next e-mail is also from February 3, 2005, but was already published by Peter Pilz on May 15, 2015 and is the only one that is available in what seems to be its original form. It's from Harald Helfrich, who informs a mr. Siegert at the BND that mr. Knau had connected an STM1-link earlier that morning (see previous e-mail). He says it contains the channels that were on the BND priority list:
This e-mail says that BND was interested in the following 2 Mbit/s channels from the Transit STM1-cable "Ffm 21 - Luxembourg 757/1":
Channel 2: Luxembourg/VG - Wien/000 750/3
Channel 6: Luxembourg/CLUX - Moscow/CROS 750/1
Channel 14: Ankara/CTÜR - Luxembourg/CLUX 750/1
Channel 50: Luxembourg/VG - Prague/000 750/1
According to Peter Pilz, additional cables were connected on February 14 and 25, as well as on March 3, 2005. Unfortunately, he either doesn't possess or didn't disclose the related e-mails, so we still don't know how many and which channels have actually been intercepted.
The interception of telephony communications therefore started in the Spring of 2005, which means that collection under Eikonal only lasted for 3 years, and not 4 years, when one would count from signing the agreement in 2004 until the end of the operation in 2008.
Ending telephone interception
Peter Pilz published the transcripts of two more e-mails, which are about ending the telephone interception. On May 27, 2008, mr. Thorwald from Deutsche Telekom sent the following message to his colleague Harald Helfrich, informing him that fully circuit-switched transit traffic isn't supported anymore. Therefore, the extraction of transit traffic at the company's premises can be terminated:
Sehr geehrter Herr Helfrich,
Wie wir bereits telefonisch besprochen, teile ich Ihnen mit, dass die Verarbeitung von reinen leitungsvermittelten "Transit-Verkehren" von uns nicht mehr durchgeführt wird.
Aus diesem Grund kann die Ableitung der Transit-Verkehre in unseren Betriebsräumen eingestellt werden.
Im leitungsvermittelten Bereich (Ableitung auf höherer Ebene) besteht aktuell der Bedarf zur Ableitung von folgenden Verkehren:
+ 2 x STM-64
+ 4 x STM-16
After that, Thorwald writes that there's currently a need to extract the traffic of two STM-64 and four STM-16 cables, which have a data rate of ca. 10 Gbit/s and 2,5 Gbit/s respectively. This is also said to be circuit-switched, but "extraction at a higher level".
Anomalies
If we assume that Peter Pilz provided the correct date for this e-mail, it's strange that there was apparently a need for new cable accesses, hardly a month before operation Eikonal was officially terminated (June 2008).
Even more strange is that the e-mail says the new accesses are also circuit-switched (leitungsvermittelt), while during the hearings it was testified that the collection of such telephone communications ended in January 2007, after Deutsche Telekom fased-out its business model for dedicated transit cables. This e-mail brings that message almost 1,5 years later!
Internet access
From the commission hearings we also learned that BND wanted access to internet traffic too, which is packet-switched (Paketvermittelt). For this, the first cable became available by the end of 2005, but it took some months before the backlink was also connected. In the spring of 2006 a second cable was added, and the front-end system and the filters were tested until mid-2007.
Could it be that mr. Thorwald just made a mistake, and wrote "leitungsvermittelten" where he meant "paketvermittelten"? But even then, why add new internet cables, just before the operation was ended?
Another question
A similar anomaly can be found in an e-mail, that according to Peter Pilz, was sent one day later, on May 28, 2008. In it, mr. Knau informed Harald Helfrich and his superior Wolfgang Alster that the access to four STM1-cables can be terminated immediately.
Given what was said during the commission hearings, one would have expected that this also had happened already in January 2007, instead of May 2008. It seems some things don't add up here.
Wie bereits fernmündlich besprochen, können nachfolgende STM1-Zuschaltungen mit sofortiger Wirkung aufgehoben werden:
Ffm 21 - Stuttgart 10 757/22A
Ffm 21 - Paris 757/1
Ffm 21 - Reims 757/1
Ffm 21 - Luxembourg 757/1
Physical cables
Unlike the numerous virtual channels in the lists, this e-mail is about physical cables. "Ffm 21 - Luxembourg 757/1" is the one mentioned in the e-mail from February 3, 2005, containing 4 channels of interest to Luxembourg; the others are cables from Frankfurt (Ffm) to Reims, Paris, and Deutsche Telekom's Point-of-Presence in Stuttgart. With this, we now have proof of 3 other cables having been tapped.
According to a list (.docx) publiced by Peter Pilz, there are 29 channels to/from Reims and 22 channels to/from Paris, all of which could easily have been in the fiber-optic cable between Frankfurt and Reims, and Frankfurt and Paris, respectively, as one single STM1-cable contains 63 separate channels:
Frankfurt - Stuttgart: ? channels of interest
Frankfurt - Paris: 22 channels of interest
Frankfurt - Reims: 29 channels of interest
Frankfurt - Luxembourg: 11 channels of interest
Peter Pilz concludes that operation Eikonal was the start of NSA's illegal mass surveillance of European telecommunications. But that's not supported by evidence. After Eikonal, NSA continued joint cable tapping operations with BND and other European agencies, but as these programs are part of RAMPART-A, they are mainly aimed at
BND cable tapping
Operation Eikonal did start something else though: it provided BND with the knowledge and the experience for conducting cable tapping on its own: in 2009 they started intercepting cables from 25 internet service providers, this time at the DE-CIX internet exchange in Frankfurt - as was revealed by Der Spiegel on October 6, 2013.
Among these 25 providers are foreign companies from Russia, Central Asia, the Middle East and North Africa, but also 6 German providers: 1&1, Freenet, Strato AG, QSC, Lambdanet and Plusserver, who almost exclusively handle domestic traffic.
It appears that this interception takes place in cooperation with the DE-CIX Management and that the various providers themselves didn't knew that this was happening. A smart move, as this provides BND with just one single point-of-contact, while the indivual providers can honestly deny that their cables are being intercepted.
Links and sources
- Heise.de: BND-Operation Eikonal: "Freibrief" für die Telekom aus dem Kanzleramt
- DerStandard.at: Pilz: Berlin genehmigte NSA-Spionage gegen Österreich
- PeterPilz.at: "Ich darf die Anregung weitergeben..." Die Operation Transit in Europa